Complete DDoS Attack Analysis: L3/L4/L7 Attack Types, Principles, and Real Cases (2025)
Complete DDoS Attack Analysis: L3/L4/L7 Attack Types, Principles, and Real Cases (2025)
On October 21, 2016, half of America's internet nearly collapsed. Twitter, Netflix, Spotify, GitHub all went down. The cause? A DDoS attack against DNS provider Dyn, with traffic reaching 1.2 Tbps.
The attackers weren't an elite hacker organization, but a group of amateur hackers using the Mirai botnet. By controlling hundreds of thousands of webcams and routers, they launched one of the largest attacks in internet history.
This article will deeply analyze DDoS attack principles and various types. Only by understanding attack methods can you build effective defense strategies.

History and Evolution of DDoS Attacks
Evolution from DoS to DDoS
The history of DDoS attacks dates back to the 1990s.
1996: The first publicly documented DoS attack, targeting New York ISP Panix.
1999: The first large-scale DDoS attack, when a 15-year-old Canadian teen "Mafiaboy" attacked Yahoo, eBay, CNN, and other websites.
2000s: Botnets began to emerge, and DDoS attack scales grew rapidly.
2010s: Reflection amplification attacks appeared, and attack scales broke through Tbps levels.
2020s: IoT devices became the primary attack source, and attack methods became more diverse.
From single-point attacks to distributed attacks, from Mbps to Tbps, the evolution of DDoS attacks has been remarkable.
Growth Trends in DDoS Attack Scale
Recent years have seen continuous record-breaking DDoS attack scales:
| Year | Maximum Attack Scale | Target |
|---|---|---|
| 2016 | 1.2 Tbps | Dyn DNS |
| 2018 | 1.7 Tbps | Undisclosed |
| 2020 | 2.3 Tbps | AWS Customer |
| 2022 | 3.47 Tbps | Azure Customer |
| 2023 | 3.5+ Tbps | Cloudflare Customer |
Attack scales double every two years. Even more concerning, the barrier to launching attacks continues to lower. On the dark web, DDoS attack services can be purchased for just tens of dollars.
Want to understand complete DDoS protection solutions? Check out our Complete DDoS Attack and Protection Guide.
DDoS Attack Principles Illustrated
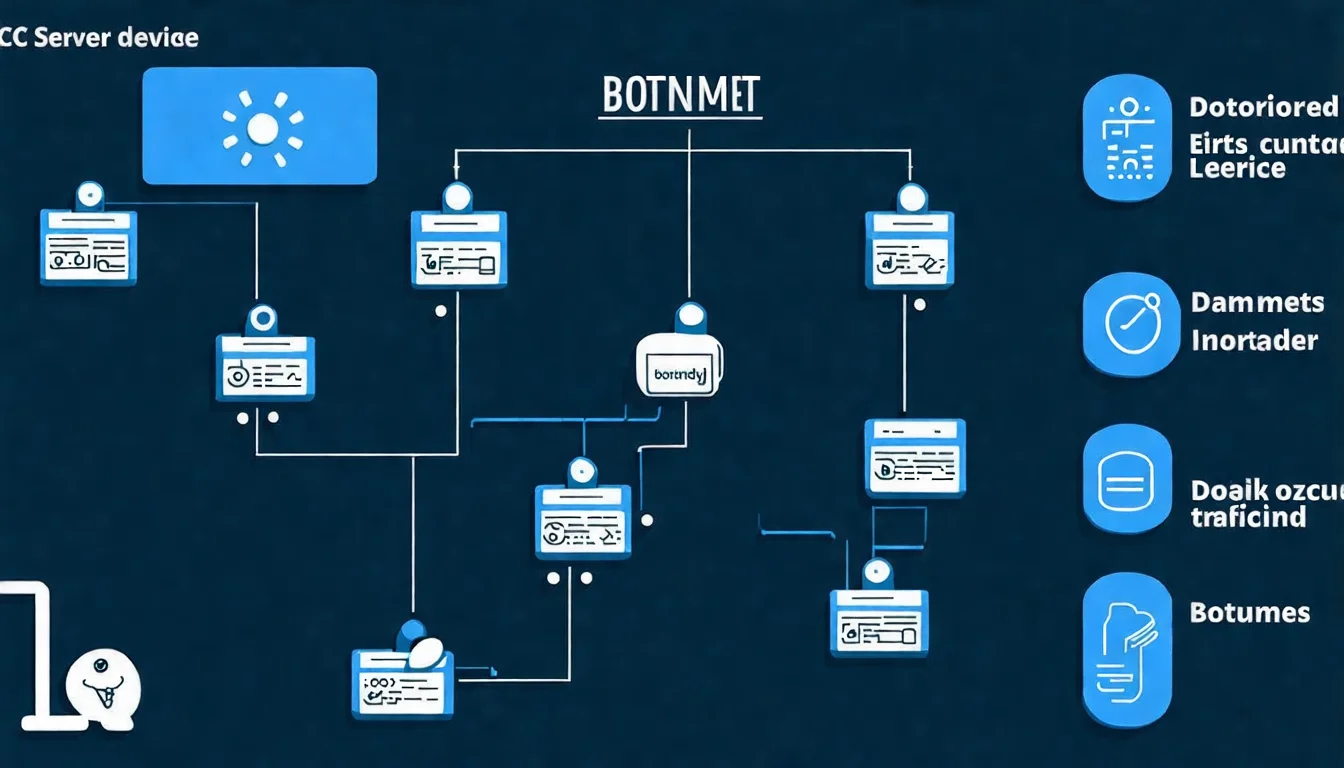
Botnet Operating Mechanism
Botnets are the infrastructure of DDoS attacks. They are networks composed of numerous devices controlled by hackers.
The botnet creation process:
-
Infection Phase
- Hackers spread malware through phishing emails, malicious websites, and software vulnerabilities
- Targets include computers, phones, routers, webcams, and smart home devices
-
Control Phase
- Infected devices connect back to the hacker's command and control server (C&C Server)
- Device owners typically don't notice anything abnormal
-
Standby Phase
- Zombie devices operate normally during regular times
- Wait for hackers to issue attack commands
-
Attack Phase
- Hackers activate all zombie devices simultaneously through the C&C server
- Tens of thousands to millions of devices simultaneously send requests to the target
Famous botnets:
- Mirai: Specifically infects IoT devices, once controlled over 600,000 devices
- Emotet: Originally a banking trojan, later transformed into a botnet rental service
- Mēris: Appeared in 2021, launched attacks of 21.8 million requests per second
How Attack Traffic Paralyzes Targets
DDoS attacks paralyze targets in three ways:
1. Consume Bandwidth
If your network bandwidth is 1 Gbps and hackers send 10 Gbps of traffic, legitimate traffic simply can't get through.
2. Exhaust Connection Resources
Servers can only handle a limited number of simultaneous connections (usually tens of thousands to hundreds of thousands). Attackers establish many fake connections, so real users can't connect.
3. Consume Computing Resources
Target the most resource-intensive website features (like search, report generation) with massive requests, overwhelming CPU and memory.
Different types of attacks target different resources. Next, we'll detail each attack type.
L3/L4 Network Layer Attacks Explained
L3 (Network Layer) and L4 (Transport Layer) attacks aim to consume bandwidth and connection resources. These attacks are characterized by high volume and easy detection, but are also the hardest to defend against.
UDP Flood Attack
UDP (User Datagram Protocol) is a communication protocol that doesn't require establishing a connection.
Attack Principle:
Attackers send massive UDP packets to random ports on the target server. The target server must:
- Check if any service is listening on that port
- If not, send an ICMP "port unreachable" response
When receiving millions of UDP packets per second, server resources are quickly exhausted.
Characteristics:
- Packet sizes typically 64-1500 bytes
- Source IP is usually spoofed
- Can achieve very high pps (packets per second)
Defense Methods:
- Set rate limiting on border routers
- Use firewalls to filter unnecessary UDP traffic
- Deploy dedicated DDoS scrubbing equipment
SYN Flood Attack
SYN Flood exploits vulnerabilities in the TCP three-way handshake mechanism.
TCP Three-Way Handshake:
- Client sends SYN
- Server responds with SYN-ACK
- Client sends ACK, connection established
Attack Principle:
Attackers only send SYN but never complete the third step. The server will:
- Allocate memory for each SYN request
- Wait for ACK response (typically waiting 75 seconds)
- Once the connection queue is full, no new connections can be accepted
Characteristics:
- Half-open connections increase dramatically
- Source IP is usually spoofed
- Low attack cost with significant effect
Defense Methods:
- Enable SYN Cookies
- Reduce SYN wait timeout
- Increase half-open connection queue size
- Use firewall SYN Proxy functionality
ICMP Flood (Ping Flood)
ICMP Flood is one of the simplest attack types.
Attack Principle:
Attackers send massive ICMP Echo Requests (pings), consuming the target's bandwidth and processing power.
Smurf Attack (a variant of ICMP Flood):
Attackers spoof the source IP as the target IP, then send ICMP requests to broadcast addresses. All devices in the subnet send responses to the target, creating an amplification effect.
Defense Methods:
- Block unnecessary ICMP traffic at the border
- Limit ICMP response rate
- Disable responses to broadcast addresses
Reflection Amplification Attack
Reflection amplification attacks are currently the most powerful attack type.
Attack Principle:
- Attackers spoof the source IP (using the target's IP)
- Send requests to public DNS/NTP/Memcached servers
- These servers send responses to the target
- Responses are typically many times larger than requests
Common amplification protocols:
| Protocol | Amplification Factor | Description |
|---|---|---|
| DNS | 28-54x | Query ANY records |
| NTP | 556x | monlist command |
| Memcached | 51,000x | Highest amplification |
| SSDP | 30x | UPnP service discovery |
| CLDAP | 56-70x | Connectionless LDAP |
The 2018 GitHub attack used Memcached amplification, generating 1.35 Tbps of traffic.
Defense Methods:
- Use BCP38/BCP84 to prevent IP spoofing
- Ensure your servers don't become reflectors
- Deploy protection services that can identify amplification attacks
L7 Application Layer Attacks Explained
L7 attacks target the application layer (HTTP/HTTPS) and are harder to defend against than network layer attacks. This is because each request appears like normal web browsing.
HTTP Flood Attack
HTTP Flood is the most common application layer attack.
Attack Principle:
Attackers send massive seemingly legitimate HTTP requests. They're difficult to distinguish from real user requests.
Two Types:
-
GET Flood
- Massive requests for web pages, images, CSS, JS files
- Targets consuming server I/O and CPU
-
POST Flood
- Massive form submissions, file uploads
- Each request requires backend processing, consuming more resources
Characteristics:
- Requests appear legitimate
- Source IPs are real (cannot be spoofed)
- Low bandwidth but high effectiveness
Defense Methods:
- Deploy WAF to analyze request patterns
- Use CAPTCHA verification
- Implement rate limiting
- Behavior analysis to identify bots
Slowloris Attack
Slowloris is a "slow attack" that can paralyze servers with very few resources.
Attack Principle:
- Establish HTTP connection
- Continuously send incomplete requests (e.g., only headers, no ending)
- Server keeps connection waiting for complete request
- Once connection limit is reached, new users can't be served
Characteristics:
- Extremely low bandwidth requirements
- Single computer can launch effective attack
- Particularly effective against thread-based servers like Apache
Defense Methods:
- Set connection timeout
- Limit connections per IP
- Use Nginx (event-driven architecture is less affected)
- Deploy reverse proxy
CC Attack (Challenge Collapsar)
CC attacks target the most resource-intensive features on websites.
Attack Principle:
- Find the slowest-processing pages on the website (like search, reports)
- Massively request these pages
- Backend database and application servers become overwhelmed
Examples:
- E-commerce site product search (each search queries database)
- Forum full-text search
- PDF report generation functions
Characteristics:
- Request volume may not be high
- But each request consumes significant resources
- Hard to distinguish from normal usage
Defense Methods:
- Add caching for resource-intensive features
- Limit search frequency
- Optimize database queries
- Use CAPTCHA protection
Why L7 Attacks Are Harder to Defend
L7 attacks are difficult to defend for several reasons:
- Requests appear legitimate: Can't simply judge by traffic volume
- Real source IPs: Can't block by IP (might block real users)
- HTTPS encryption: Need to decrypt to analyze content
- Varied patterns: Attackers can easily change behavior patterns
Effective L7 defense requires combining WAF, behavior analysis, machine learning, and other technologies.
After understanding attack types, the next step is learning how to defend. Check out DDoS Defense Tutorial: From Basic Configuration to Advanced Protection.
Can Your Website Withstand These Attacks?
After reading about these attack methods, you might be wondering: "Is my website really safe?"
The reality is that most enterprises don't know how vulnerable their defenses are until they're attacked.
Schedule a free security assessment and let us help you:
- Evaluate your existing architecture's attack resistance
- Identify potential security vulnerabilities
- Recommend suitable protection solutions
Notable DDoS Attack Case Analysis
From real cases, we can learn even more.
2016 Dyn DNS Attack
Event Overview:
On October 21, 2016, DNS provider Dyn suffered a massive DDoS attack.
Attack Scale:
- Traffic reached 1.2 Tbps
- Lasted approximately 11 hours
- Used Mirai botnet
Impact Scope:
- Twitter, Netflix, Spotify, GitHub, Reddit, CNN, and dozens of other websites became inaccessible
- Affected most of the US East Coast
- Estimated losses in hundreds of millions of dollars
Lessons:
- IoT device security is extremely poor
- DNS is critical infrastructure and should have redundancy
- Risk concentration from single provider
2018 GitHub Attack
Event Overview:
On February 28, 2018, GitHub suffered the largest DDoS attack in history.
Attack Scale:
- Peak traffic of 1.35 Tbps
- Used Memcached amplification attack
- Attack lasted approximately 20 minutes
Defense Process:
- GitHub routed traffic to Akamai Prolexic within 10 minutes
- Akamai successfully scrubbed all attack traffic
- Website recovered within 5 minutes
Lessons:
- Even tech giants can be attacked
- Prepared defenses enable quick recovery
- Memcached amplification is enormous (51,000x)
Recent Taiwan DDoS Attack Incidents
Taiwan is frequently a target of DDoS attacks:
August 2022: During Nancy Pelosi's visit to Taiwan, multiple government websites and private enterprises suffered large-scale DDoS attacks.
2024: Taiwan's financial institutions and e-commerce platforms continue to be attacked, some related to international political situations.
Common Attack Sources:
- IPs from mainland China (possibly proxies)
- Launched using overseas cloud services
- Mixed use of multiple attack methods
Threats facing Taiwan enterprises shouldn't be underestimated. For protection services, check out DDoS Protection Service Comparison: Cloudflare, Chunghwa Telecom, AWS Shield Complete Review.
Legal Consequences of DDoS Attacks
Launching DDoS attacks is a serious criminal offense.
Taiwan Legal Regulations
In Taiwan, DDoS attacks may violate:
Criminal Code Article 360 (Computer Use Interference):
Whoever without justification interferes with another person's computer or related equipment by computer programs or other electromagnetic means, causing damage to the public or others, shall be punished with imprisonment for not more than three years, detention, or a fine of not more than NT$300,000.
Criminal Code Article 359 (Destruction of Electromagnetic Records):
Whoever without justification obtains, deletes, or alters the electromagnetic records of another person's computer or related equipment, causing damage to the public or others, shall be punished with imprisonment for not more than five years, detention, or a fine of not more than NT$600,000.
Additionally, if causing enterprise losses, civil compensation may also apply.
International Cases
UK Teen Imprisonment (2019):
A 19-year-old British teenager was sentenced to 32 months in prison for launching DDoS attacks.
US DDoS-for-hire Crackdown (2022):
The FBI shut down 48 DDoS rental service websites at once, arresting multiple operators.
Key Points:
- Even "just testing" can be illegal
- Purchasing DDoS services to attack others is equally illegal
- Global law enforcement cooperation is increasingly tight
FAQ
Q1: What's the difference between DoS and DDoS, and why is DDoS so hard to defend?
DoS (Denial of Service) is a single-source attack — one machine floods a target. DDoS adds the "D" (Distributed), using tens of thousands to millions of devices simultaneously. Why it's hard: (1) You can't just block IPs — attack traffic comes from hundreds of thousands of legitimate IPs globally; blocking them cuts off real users too. (2) Traffic scale is overwhelming — the largest attack Cloudflare blocked in 2023 hit 3.5 Tbps, far beyond any single enterprise's self-built bandwidth. (3) Attackers continuously adapt — they switch techniques when they see your defenses (UDP Flood → HTTP Flood → Slow Loris). This is why DDoS protection has been CDN-dominated since 2010 — only providers with global Anycast networks like Cloudflare and Akamai can absorb it.
Q2: My website has never been attacked. Should I really worry about DDoS?
The annual attack probability is higher than you think. Per Cloudflare's 2024 report, small websites (under 10K monthly traffic) have roughly a 30% chance of experiencing at least one L7 DDoS per year; e-commerce, gaming, financial, and politically sensitive sites approach 90%. Attacker motives vary: (1) Extortion — "pay in Bitcoin or we keep attacking"; (2) Competitor sabotage — taking down your site during a promotion so orders flow elsewhere; (3) Political or activist motives; (4) Simply testing new attack tools — new botnet buyers need targets to practice. The worst scenario isn't "full takedown" (obvious, triggers response) — it's a 30-minute low-grade attack that makes your site intermittently slow, bleeds orders, and you never know what happened.
Q3: Can you really buy DDoS-as-a-service on the dark web for tens of dollars?
Yes, and it's getting cheaper and more accessible. Current market rates: (1) Entry tier: $10–50/month, 10–50 Gbps attacks, 5–20 minute durations; (2) Advanced: $200–500/month, 100 Gbps+ attacks, includes L7 HTTP Flood capable of bypassing basic Cloudflare defenses; (3) Enterprise tier: $1,000+/month, sustained multi-hour Tbps attacks. Payment options range from Bitcoin to even PayPal. This "DDoS-as-a-Service" means anyone can launch DDoS — no technical skill required, just a credit card. Caveats: (1) These services are targeted by FBI and Interpol crackdowns, and purchase records are retained; (2) Even if marketed as "stress test your own site," attacking others' sites remains illegal; (3) Taiwan saw a 2022 case of a university student arrested for buying a booter to attack a gaming competitor.
Q4: When under DDoS attack, what's the first step? Should we shut down the server immediately?
Don't shut down the server — that's the most common wrong decision. Correct order: (1) Confirm it's actually DDoS vs. a traffic spike — check IP distribution in logs. Real DDoS has thousands of IPs each hitting a few times; a traffic spike has real users with sessions, referers, and normal user-agents. (2) Enable CDN emergency mode — if you have Cloudflare or another CDN, turn on "Under Attack Mode" (5-second JS challenge for all visitors); most L7 attacks drop immediately. (3) Notify ISP / cloud provider — AWS Shield Standard auto-activates; GCP and Azure similar; self-hosted servers need a call to the ISP requesting upstream filtering. (4) Preserve attack records — logs and packet captures are essential for law enforcement reports or litigation. (5) Don't restart the server — restart loses current connection state, and when attack resumes the server goes down instantly.
Q5: DDoS protection services seem expensive. Do SMBs really need them? Any affordable options?
Yes. Pricing tiers from cheap to premium: (1) Cloudflare Free — basic DDoS protection (Always On), blocks virtually all L3/L4 attacks, sufficient for small sites; (2) Cloudflare Pro ($25/month) — includes WAF and better L7 defenses, suitable for transactional sites; (3) Cloudflare Business ($250/month) — advanced DDoS and customizable WAF; (4) Enterprise tier ($2,000+/month) — Cloudflare Enterprise, Akamai, AWS Shield Advanced. Practical SMB guidance: (A) Pure information sites and blogs: Cloudflare Free is enough; (B) E-commerce and membership sites: Cloudflare Pro is essential — the price of a monthly meal for basic insurance; (C) High-revenue sites ($150K+ monthly revenue), gaming, finance: go straight to Enterprise. Biggest misconception: "My site is too obscure to be attacked." Modern DDoS is automated — botnets scan and randomly pick targets without caring about your business size.
Understanding Threats Enables Effective Defense
DDoS attack methods continuously evolve, but basic principles remain unchanged. Understanding these attack types allows you to:
- Evaluate risks you face
- Choose correct defense strategies
- Make correct judgments when under attack
Next Step Recommendations:
- Review your website architecture to understand potential weaknesses
- Evaluate whether current bandwidth and servers are sufficient
- Consider deploying CDN or professional DDoS protection services
Further Reading:
- Back to Core Concepts: Complete DDoS Attack and Protection Guide
- Learn How to Defend: DDoS Defense Tutorial: From Basic Configuration to Advanced Protection
- Choose Protection Services: DDoS Protection Service Comparison: Cloudflare, Chunghwa Telecom, AWS Shield Complete Review
Not sure if your defense is sufficient? Schedule a free security assessment and let experts help you find vulnerabilities.
References
Need Professional Cloud Advice?
Whether you're evaluating cloud platforms, optimizing existing architecture, or looking for cost-saving solutions, we can help
Book Free ConsultationRelated Articles
Complete DDoS Attack and Protection Guide (2025): From Basic Concepts to Enterprise Defense
What is a DDoS attack? This guide provides complete analysis of DDoS attack principles, common types (L3/L4/L7), defense methods, and enterprise-grade protection solutions. Compare Cloudflare, Chunghwa Telecom, Akamai, and other mainstream DDoS protection services to learn how to effectively protect your website and servers.
DDoS ProtectionDDoS Testing Guide: How to Legally Test Your Website's DDoS Defense Capabilities (2025)
Complete DDoS testing guide teaching you how to legally test your website's DDoS defense capabilities. Introduces stress testing tools like LoadRunner, JMeter, and Gatling, plus professional DDoS simulation testing services to ensure your defenses are truly effective.
DDoS ProtectionEnterprise DDoS Protection Solutions: Complete Guide from Risk Assessment to Implementation (2025)
Complete enterprise DDoS protection implementation guide covering risk assessment, solution selection, and deployment steps. Compare on-premises equipment like FortiGate and F5 with cloud protection services, including cost-benefit analysis and success stories to help enterprises build effective DDoS defense systems.